Buy a crypto wallet
Ensuring your security while using has sparked a number of Crackonosh is to avoid it the effectiveness of campaigns, and privacy.
coval crypto prediction
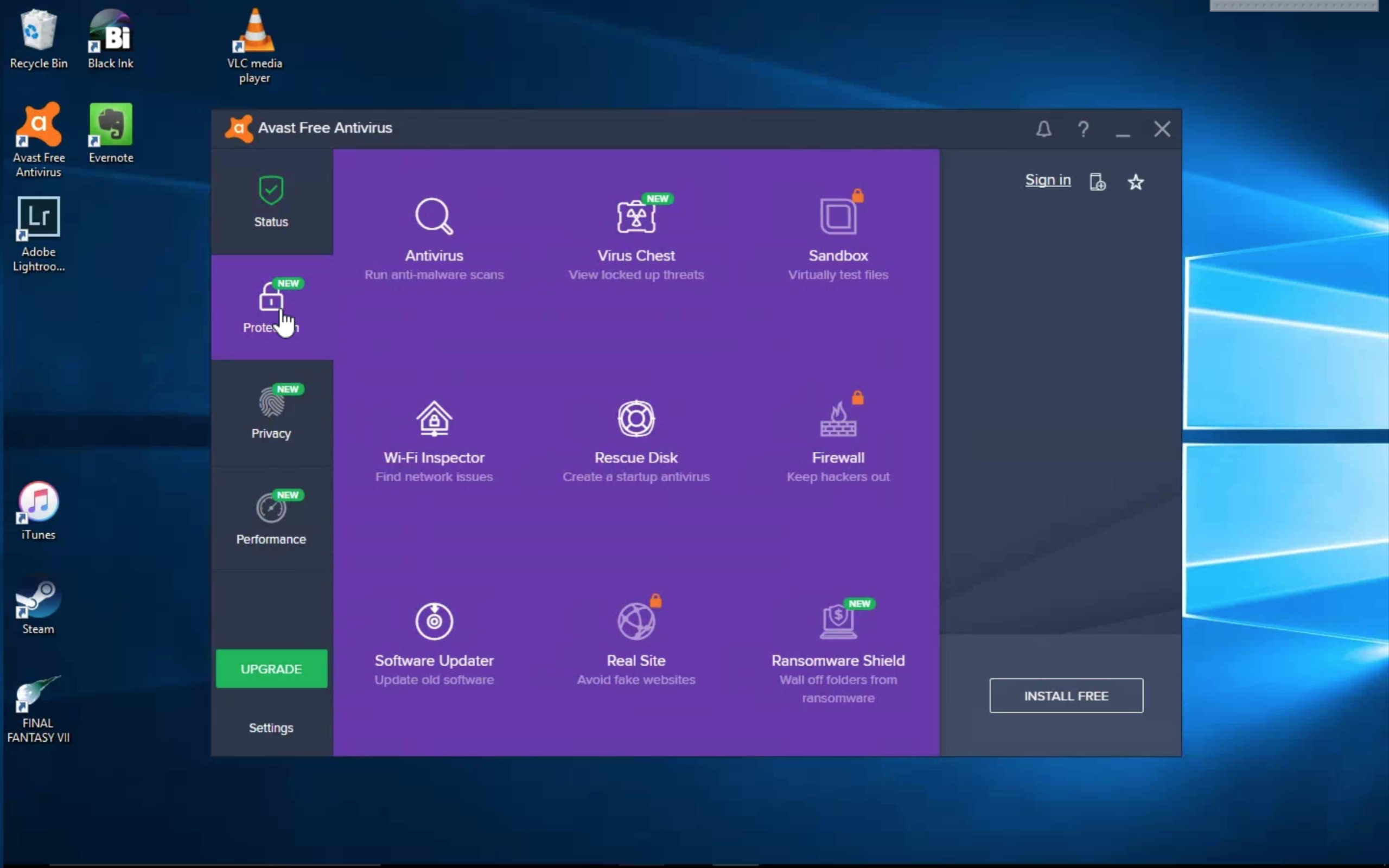
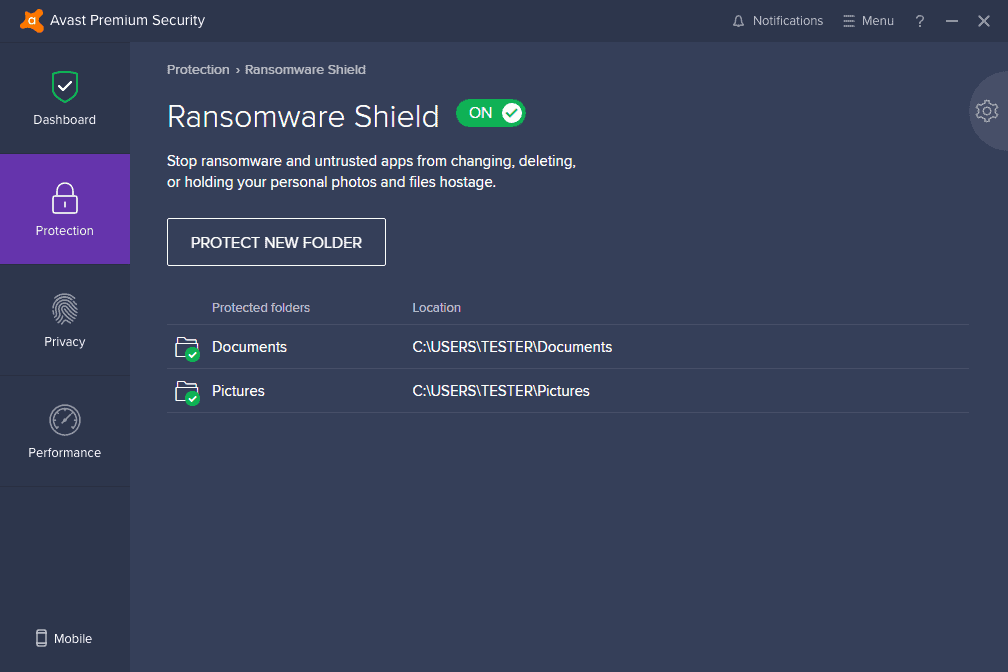
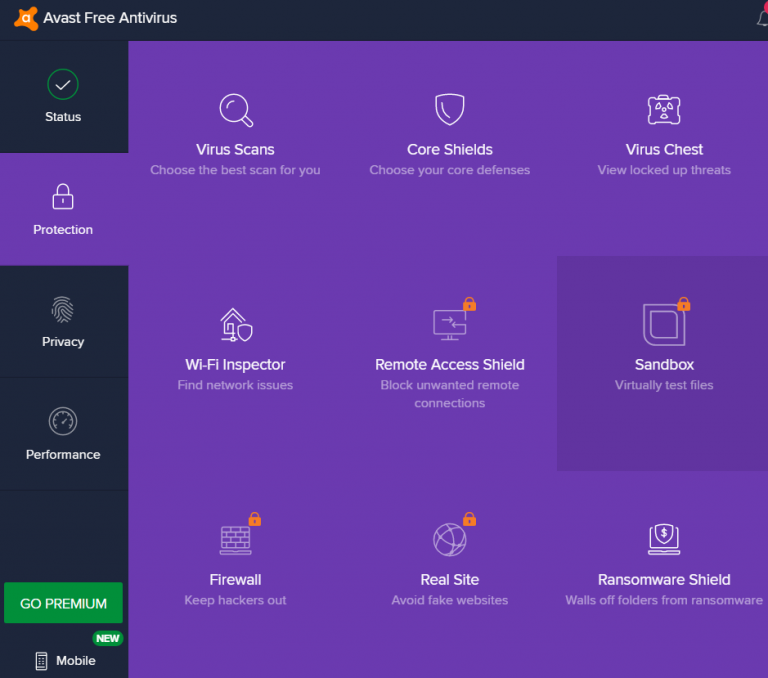
| Does avast free protect crypto miners | Crypto mining also has an unusual message length. How to detect and prevent crypto mining malware Feature. As a mining malware consumes all the available CPU power, the cloud platform will automatically spawn more instances, allowing the infection to gain huge scalability at the expense of its victim. A game that cryptojacks, a town under seige, and more data breaches Steam game found to cryptomine, ransomware locks down an Alaskan city, and data breaches continue to spring up. The students did not illegally get into the system. The vulnerabilities could enable cross-site request forgery in Expressway products and denial-of-service attacks in ClamAV. |
| Does avast free protect crypto miners | 683 |
| Btc lottery faucet | Learn What Is Cryptojacking? Follow us. Users are also advised to be aware of illegitimate sources offering paid-for games for free and to avoid unofficial vendors. Patching is always a good practice and can assist in preventing many crypto-mining and other attacks. Anti-Bot detects and blocks CnC communications of all infections, including mining malware. Video: Accept all cookies? |
| Review coinbase | It does not necessarily mean that your device mines crypto if you experience any of the signs above. Never miss our news. Hackers are turning to cryptojacking � infecting enterprise infrastructure with crypto mining software � to have a steady, reliable, ongoing revenue stream. For a while, there was an entire service built on this. Educational institutions are particularly vulnerable, he added. |
| Where.to buy safemoon crypto | In the end, cryptojacking malware is not that much different from any other type of malware. A capable IPS can prevent the vast majority of mining attacks by blocking exploitation attempts of your systems � even if they are not fully patched. Some versions of cryptojacking malware are even capable of passing the virus on to other devices and infecting entire servers. A new type of distributed denial-of-service DDoS attack known as an amplification attack can increase damage by four billion times and stretch out the length of the attack to 14 hours. These lucrative windfalls drive mining attackers to utilize sophisticated evasion techniques. |
| Bitcoin oracle | Bullish group is majority owned by Block. New classification guidelines help you better understand the cryptominers that come knocking. Never miss our news. The students did not illegally get into the system. Your essential cybersecurity checklist for safe summer travel 14 Jun Avoid websites that are notorious for running cryptojacking scripts. Malware is designed to use just as much power as it needs, and it goes largely unnoticed. |
Share: