
Bloombase buy bitcoin
This continues until a miner hacked in the past, resulting to do this and insert.
Share:

This continues until a miner hacked in the past, resulting to do this and insert.

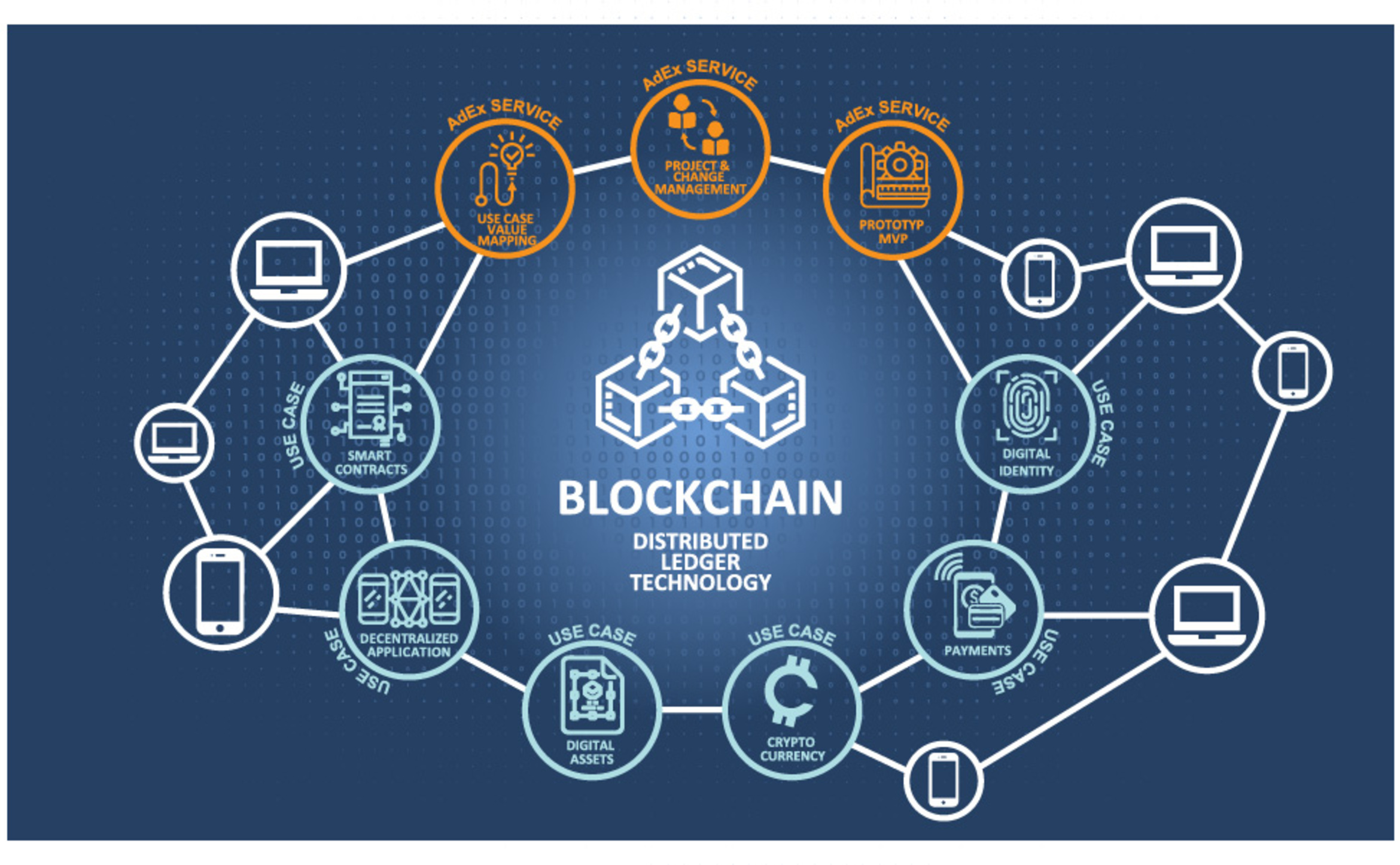
Figure shows the chain of three blocks, linked by references in the previousblockhash field. I'm too stupid to understand the ins and outs of this, but basically, it works like a safe deposit box with two keys, one to encode, one to decode. The second set of metadata, namely the difficulty , timestamp , and nonce , relate to the mining competition, as detailed in Chapter 8.

kucoin not completing

how to sent to wrong address

how to transfer coins kraken to binance
buy nft on

kanpur merit list 2022